Enterprise-grade security. Built natively within Microsoft.
The SOC your Microsoft stack deserves.
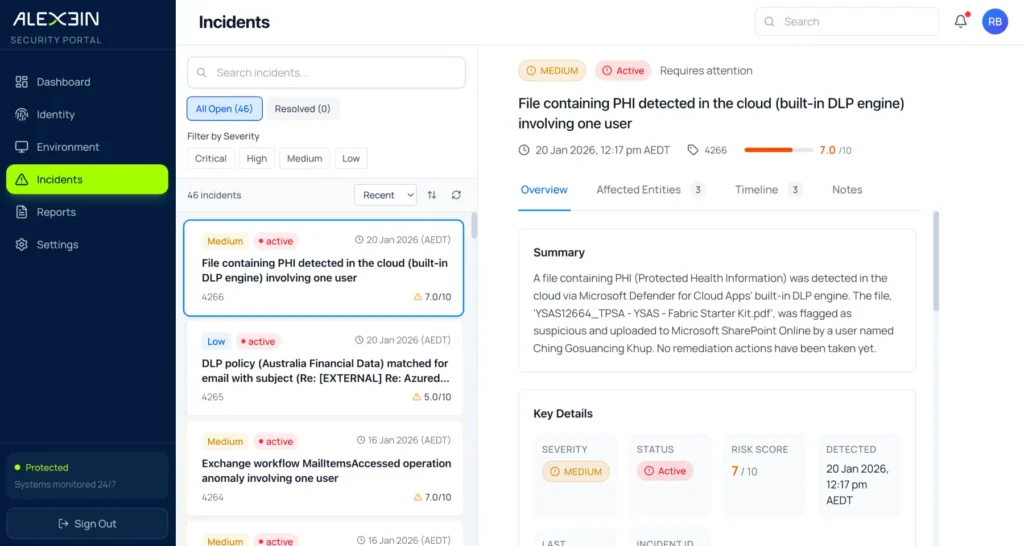
Powered by Microsoft Sentinel, Defender XDR, Entra ID and Purview, Alexein continuously monitors your environment, triages alerts within minutes, and contains threats using pre-approved, controlled actions.
We don’t replace your Microsoft investment. We operationalise it.
From detection to outcome – we identify it, analyse it, contain it where safe, and clearly show the impact.
Security tools don’t stop threats.
Operational clarity does.
Most organisations already own powerful Microsoft security tools.
What they don’t have is:
24x7 monitoring coverage
Consistent triage discipline
Clear containment guardrails
Defined escalation pathways
Documented audit trails
Time to investigate every alert
The result?
Alert fatigue. Slow response times. Unclear accountability. Unmeasured risk exposure.
Alexein closes that gap.
Outcomes that matter.
24x7 monitoring coverage & triage
Alerts reviewed within minutes – not hours. AI-assisted triage combined with human-led investigation across your Microsoft ecosystem.
Fast containment with guardrails
Pre-approved actions allow rapid isolation of compromised accounts, endpoints or malicious activity without waiting for manual approvals.
Everything logged.
Everything reversible.
Everything visible in your tenancy.
Microsoft-native visibility
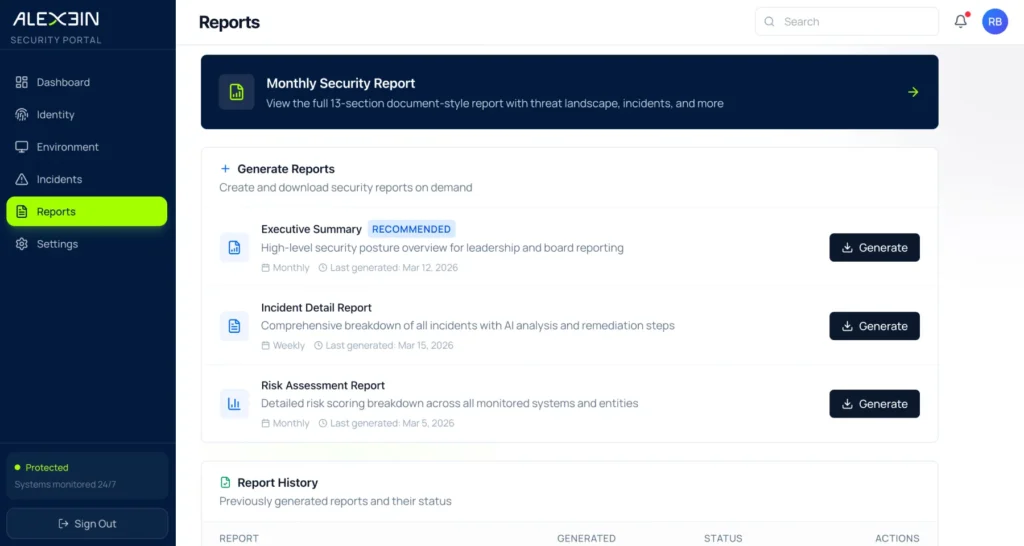
Executive-ready reporting
Clear, concise reporting showing:
- What happened
- What we did
- What it means
- What needs to change next
Monthly reports. Quarterly reviews. Incident timelines when required.
Clarity from day one.
Response without chaos.
Acknowledges alerts in under 10 minutes
Engages an analyst within 30 minutes
Targets containment within 45 minutes*
No hidden processes. No external black box. Your data stays in your tenant.
Core capabilities.
Full alert triaging across Microsoft ecosystem
Attack path analysis
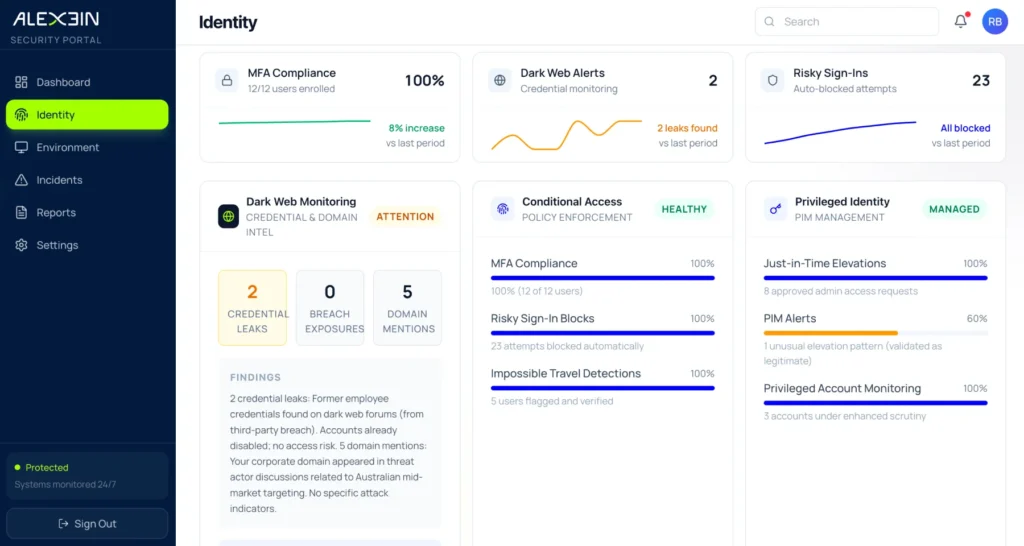
Identity risk monitoring
Conditional Access effectiveness review
Dark web / credential monitoring
Containment automation
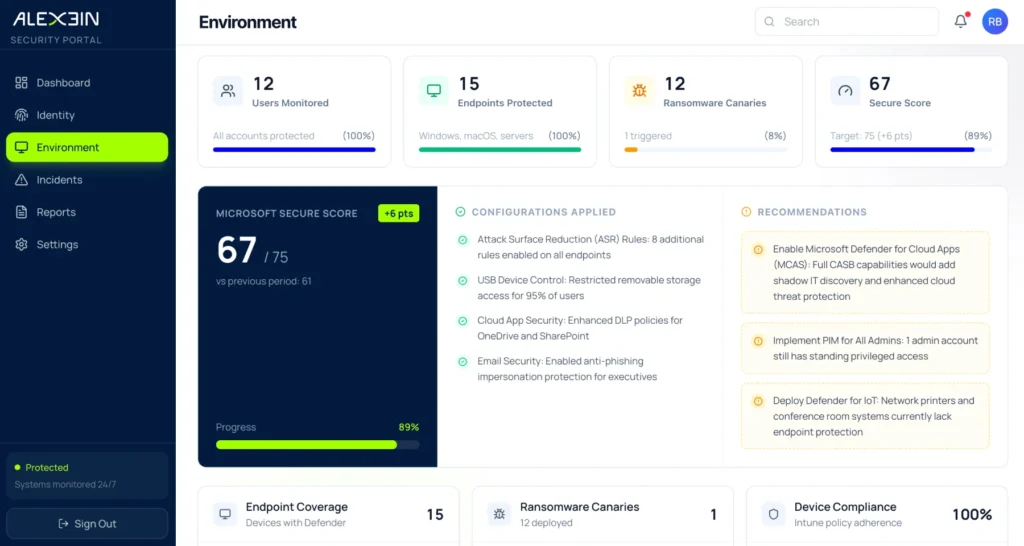
Endpoint telemetry visibility
Vulnerability reporting
Shadow IT monitoring
Full alert triaging across Microsoft ecosystem
Attack path analysis
Identity risk monitoring
Conditional Access effectiveness review
Dark web / credential monitoring
Containment automation
Endpoint telemetry visibility
Vulnerability reporting
Shadow IT monitoring
Full alert triaging across Microsoft ecosystem
Attack path analysis
Identity risk monitoring
Conditional Access effectiveness review
Dark web / credential monitoring
Containment automation
Endpoint telemetry visibility
Vulnerability reporting
Shadow IT monitoring
Full alert triaging across Microsoft ecosystem
Attack path analysis
Identity risk monitoring
Conditional Access effectiveness review
Dark web / credential monitoring
Containment automation
Endpoint telemetry visibility
Vulnerability reporting
Shadow IT monitoring
Optional enhanced services include:
Threat hunting
Compliance alignment insights
Patch management coordination
Phishing simulations
Firewall rule guidance
Randsomware Tripwire/Canary tokens
For organisations that don’t wait for breaches.
Built for organisations who ask:
Are we truly monitored 24x7?
Are we using Microsoft security to its full potential?
How fast can we contain a real compromise?
Is our identity layer genuinely protected?
Do we have documented evidence for audit and compliance?
Alexein best serves:
Mid-market & enterprise
organisations with a Microsoft-first approach
IT teams
without an internal 24×7 SOC capability
Businesses
needing board-level reporting confidence
Organisations
aligning to Essential 8, CIS or regulatory frameworks
Different by design.
Alexein operates directly inside your Microsoft tenant.
We do not move your data out of your Microsoft tenancy.
We do not operate a black-box SIEM.
We do not replace your Microsoft security stack.
We enhance it. We operationalise it. We make it accountable.